Cyber: Breaking: Inside The Remus Infostealer: Session Theft, Maas, And Rapid E...
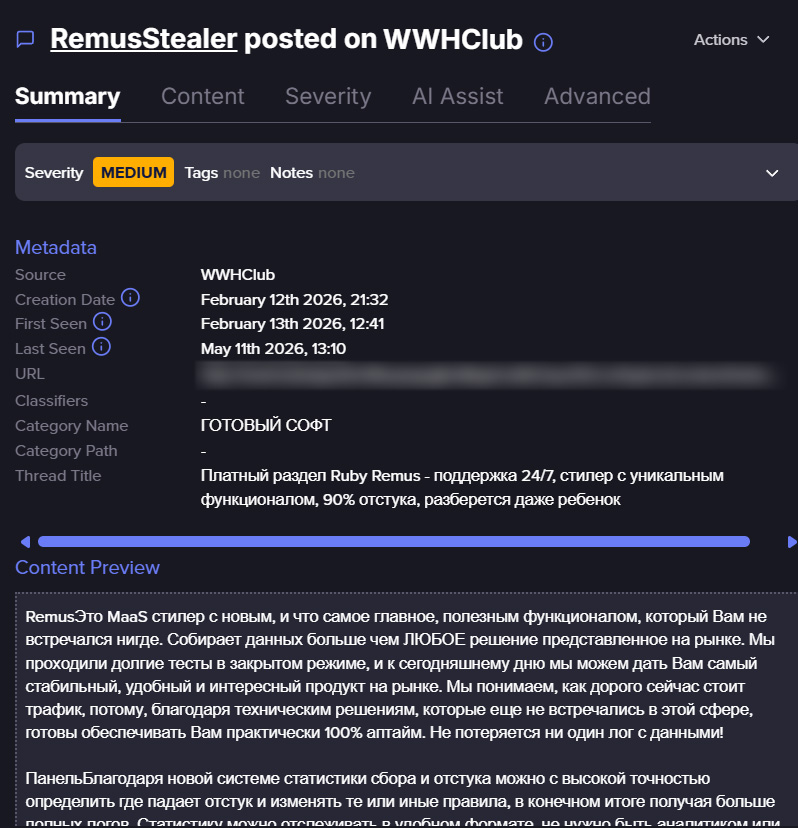
In recent months, a new infostealer malware known as REMUS has emerged across the cybercrime landscape, drawing attention from security researchers and malware analysts. Several technical analyses published in recent months focused on the malware’s capabilities, infrastructure, and similarities to Lumma Stealer, including browser targeting mechanisms, and credential theft functionality and more. However, far less attention has been given to the underground operation behind the malware itself. The findings reveal not only the rapid evolution of the stealer’s capabilities, but also a growing focus on commercialization, operational scalability, session theft, and password-manager targeting. More broadly, the activity offers insight into how modern malware-as-a-service (MaaS) operations increasingly resemble structured software businesses, with continuous development cycles, operational refinements, and features designed to improve usability, persistence, and long-term monetization. The underground activity reveals a highly compressed but aggressive development cycle, with the operator repeatedly publishing feature updates, operational refinements, and new collection capabilities over just a few months. Rather than advertising a static malware build, the posts portray an actively maintained MaaS platform evolving in near real time. March 2026 represented the campaign’s most active development period. During this phase, the operator introduced restore-token functionality, expanded log handling, worker tracking, statistics pages, duplicate-log filtering, and improved Telegram delivery workflows. Multiple posts focused not on theft itself, but on operational visibility and campaign management. One update added worker nicknames to log tables and statistics views, while another improved loader execution visibility so operators could better understand failed infections. The shift suggests REMUS was evolving into a broader operational platform rather than just a malware executable. April 2026 showed a clear move toward session continuity and browser-side authentication artifacts. The operator added SOCKS5 proxy support, improved token restoration, anti-VM toggles, gaming-platform targeting, and password-manager-related collection. One update explicitly stated: “Added IndexedDB collection for 1Password and LastPass extensions.” Another referenced Bitwarden-related searches. The posts increasingly emphasized authenticated sessions, restore workflows, and browser
Source: BleepingComputer