Cyber: Complete Guide to Google Chrome adds infostealer protection against session cookie theft
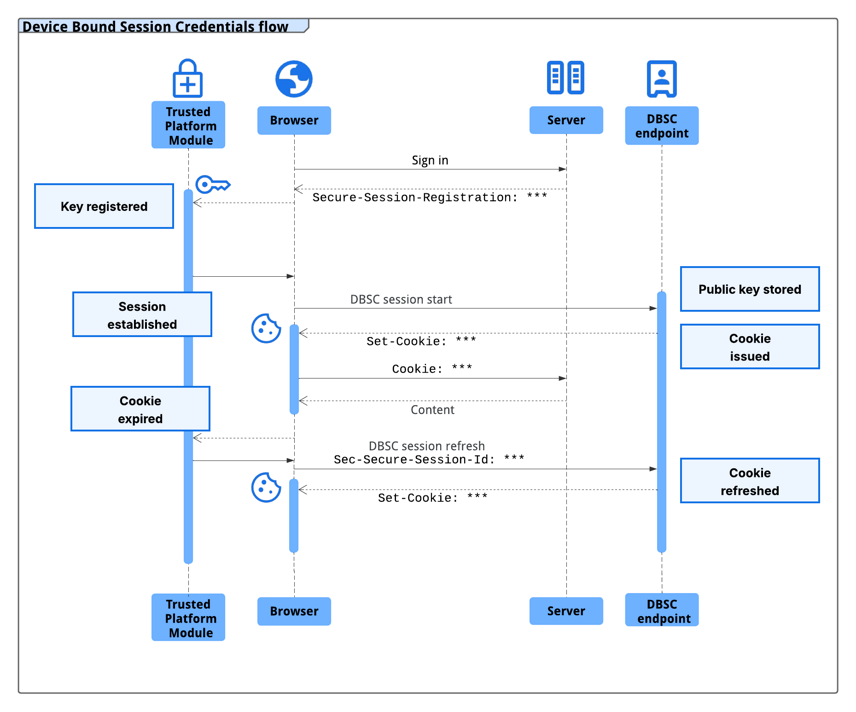
macOS users will benefit from this security feature in a future Chrome release that has yet to be announced. The new protection has been announced in 2024, and it works by cryptographically linking a user's session to their specific hardware, such as a computer's security chip - the Trusted Platform Module (TPM) on Windows and the Secure Enclave on macOS. Since the unique public/private keys for encrypting and decrypting sensitive data are generated by the security chip, they cannot be exported from the machine. This prevents the attacker from using stolen session data because the unique private key protecting it cannot be exported from the machine. Google says that multiple infostealer malware families, like LummaC2, “have become increasingly sophisticated at harvesting these credentials,” allowing hackers to gain access to users’ accounts. The DBSC protocol was built to be private by design, with each session being backed by a distinct key. This prevents websites from correlating user activity across multiple sessions or sites on the same device. Additionally, the protocol enables minimal information exchange that requires only the per-session public key necessary to certify proof of possession, and does not leak device identifiers. In a year of testing an early version of DBSC in partnership with multiple web platforms, including Okta, Google observed a notable decline in session theft events.
Source: BleepingComputer