Cyber: Inside an Underground Guide: How Threat Actors Vet Stolen Credit Card Shops (2026)
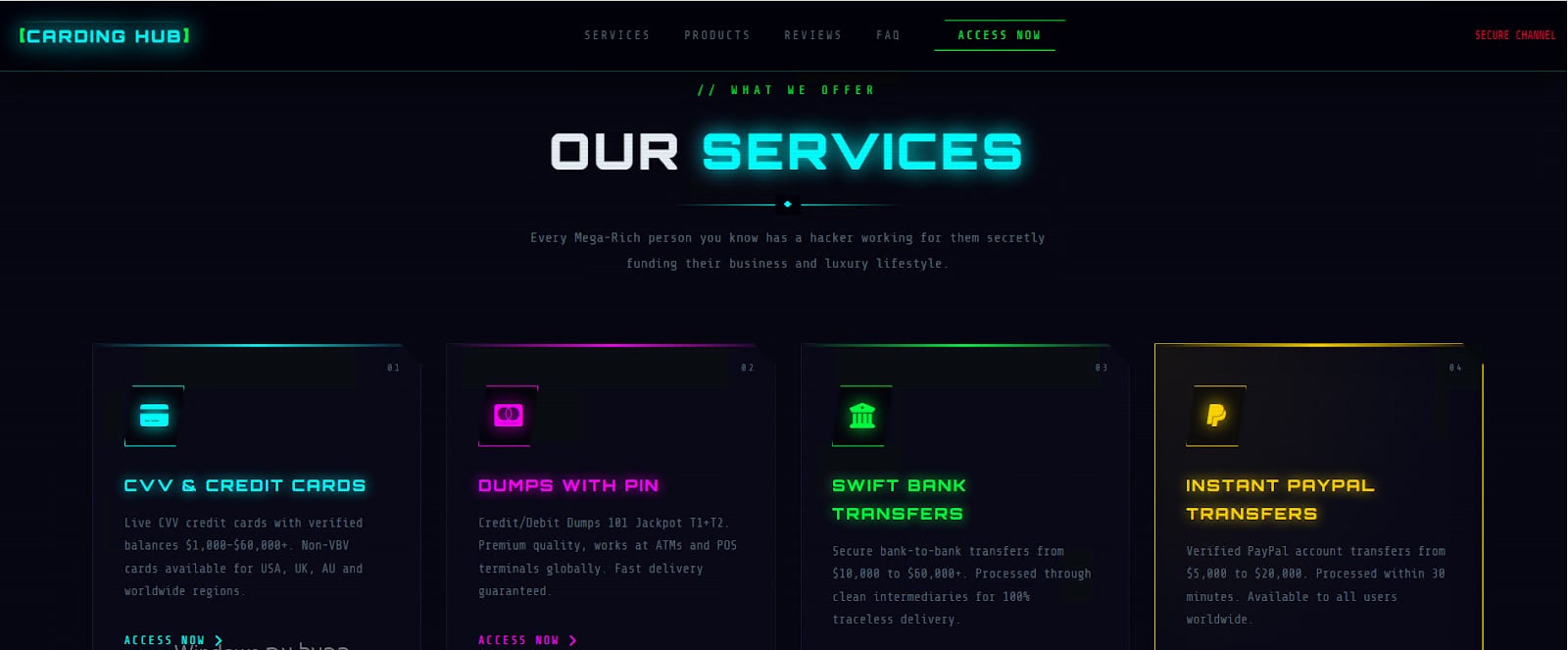
The underground market for stolen credit card data has long operated as a volatile and highly deceptive ecosystem, where even experienced actors routinely fall victim to scams, exit schemes, and compromised services. In recent years, this environment has become even more unstable, driven by increased law enforcement pressure, internal distrust among criminals, and the rapid turnover of marketplaces. As a result, threat actors are increasingly forced to adopt more structured approaches to identifying reliable suppliers and minimizing risk within their own illicit operations. A guide found on an underground forum by Flare analysts sheds light on how threat actors themselves navigate the volatile world of credit card (CC) marketplaces. The document, titled “The Underground Guide to Legit CC Shops: Cutting Through the Bullshit”—provides a structured look at how actors attempt to reduce risk in an ecosystem plagued by scams, law enforcement infiltration, and short‑lived operations. Analysis of the guide reveals more than just practical advice. It outlines a methodology for vetting carding shops, operational security practices, and sourcing strategies, effectively documenting how today’s fraud actors think about trust, reliability, and survivability. While parts of the guide appear to promote specific services, suggesting a possible vested interest from its author, it still offers a valuable glimpse into the inner workings of the carding economy, and the evolving standards actors use to operate within it. One of the most striking aspects of the guide is how it reframes carding from opportunistic fraud into a process‑driven discipline. Rather than focusing on how to use stolen cards, the document emphasizes how to evaluate suppliers. This shift reflects a broader evolution within underground markets, where the primary risk is no longer just operational failure, but being defrauded by other criminals or interacting with compromised infrastructure.
Source: BleepingComputer