Cyber: Recently leaked Windows zero-days now exploited in attacks
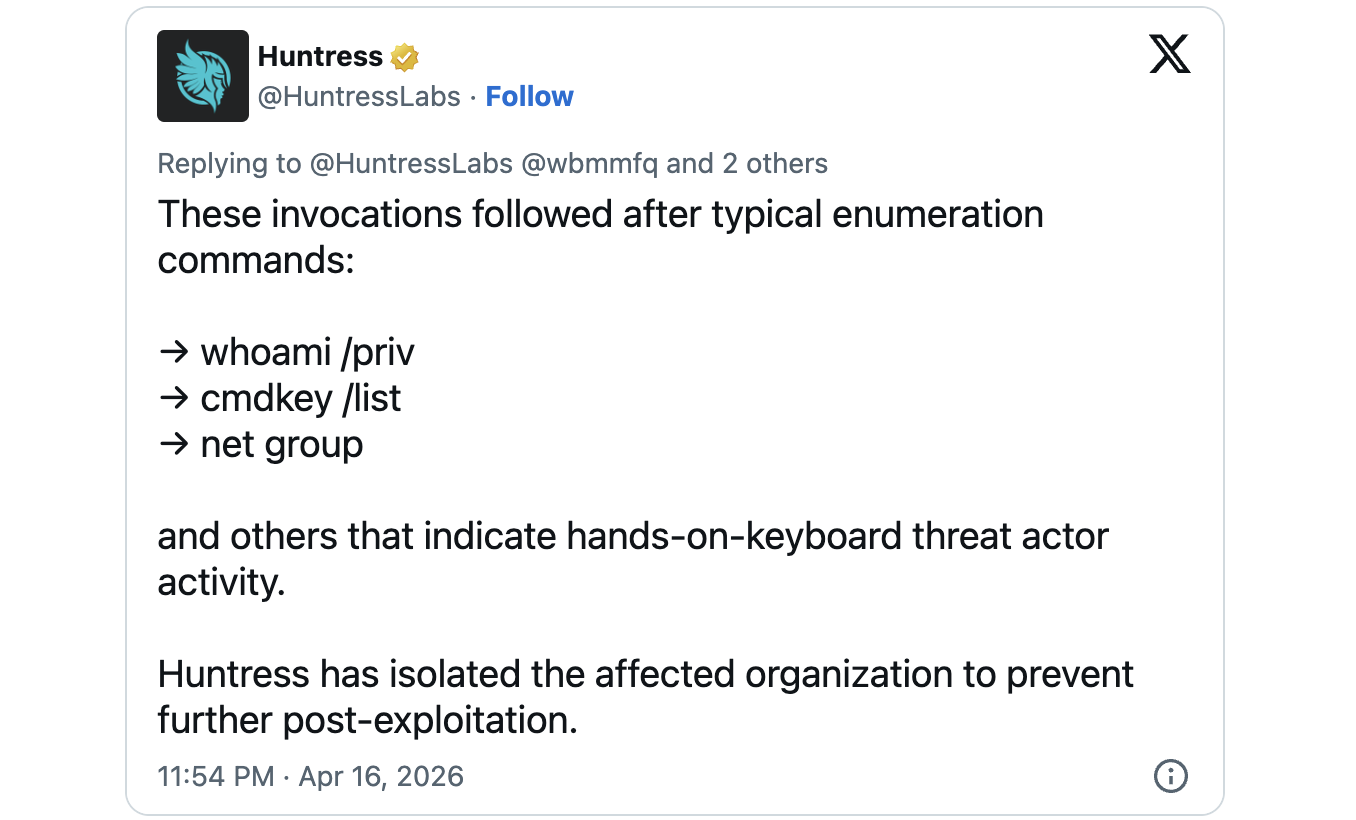
Threat actors are exploiting three recently disclosed Windows security vulnerabilities in attacks aimed at gaining SYSTEM or elevated administrator permissions. Since the start of the month, a security researcher known as "Chaotic Eclipse" or "Nightmare-Eclipse" has published proof-of-concept exploit code for all three security issues in protest to how Microsoft's Security Response Center (MSRC) handled the disclosure process. Two of the vulnerabilities (dubbed BlueHammer and RedSun) are Microsoft Defender local privilege escalation (LPE) flaws, while the third (known as UnDefend) can be exploited as a standard user to block Microsoft Defender definition updates. At the time of the leak, the security flaws these exploits targeted were considered zero-days by Microsoft's definition, since they had no official patches or updates to address them. On Thursday, Huntress Labs security researchers reported seeing all three zero-day exploits deployed in the wild, with the BlueHammer vulnerability being exploited since April 10. They also spotted UnDefend and RedSun exploits on a Windows device that was breached using a compromised SSLVPN user, in attacks showing evidence of "hands-on-keyboard threat actor activity." "The Huntress SOC is observing the use of Nightmare-Eclipse's BlueHammer, RedSun, and UnDefend exploitation techniques," the researchers said. While Microsoft is now tracking the BlueHammer vulnerability as CVE-2026-33825 and has patched it in the April 2026 security updates, the other two flaws remain unaddressed.
Source: BleepingComputer