Cyber: The Browser Is Breaking Your Dlp: How Data Slips Past Modern C... (2026)
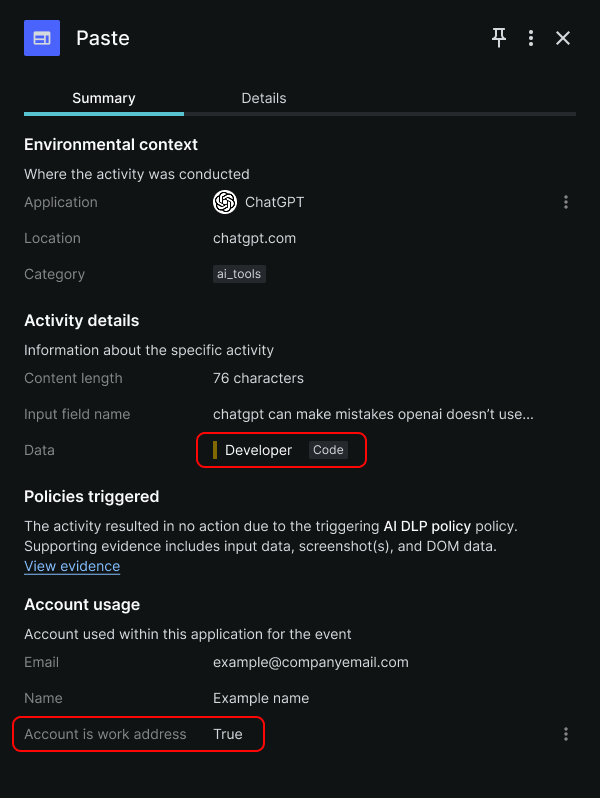
Preventing sensitive data loss has historically been treated as an endpoint or network problem. Deploy an agent, inspect files, monitor traffic, and you have coverage—or so you think. Our recent analysis shows that 46% of sensitive file uploads to web apps are sent to unsanctioned accounts, exposing a significant gap in how organizations monitor and control the flow of data moving throughout their digital ecosystem. Security teams think they have significant DLP coverage, but they’re actually lacking visibility and control into where data is often moving today: in the browser. Enterprise workflows have shifted from software on the endpoint to browser-based applications. Today, employees commonly use Google Workspace, Microsoft 365, or Salesforce; developers utilize GitHub, Jira, and internal web apps; and many departments now embrace AI tools like ChatGPT and copilots. Instead of downloading, modifying, and re-uploading files to sanctioned web apps, users are interacting with data directly in the browser by copying data from or between applications, uploading files to various tools, and inputting data into web forms and AI prompts. Compounding the risks of these activities is the simple fact that employees often use personal accounts and unsanctioned instances without restriction. In other words, the traditional DLP controls your team relies on aren’t instrumented where much of the modern activity is happening. See how Keep Aware protects sensitive data directly in the browser—without slowing your team down. Get real-time visibility, smart alerts, and seamless control over data movement across AI tools and other apps. Book a demo to see browser-native data loss prevention in action. To understand why existing DLP implementations are falling short, it’s important to look at how data leakage actually occurs in modern environments. Within browser sessions, users can type, paste, and upload data to web pages and applications—both sanctioned and not.
Source: BleepingComputer