How A CPU Spike Led To Uncovering A Ransomhub Ransomware Attack
Varonis recently helped a customer who observed a spike in CPU activity on a server in their environment, where a shallow review of the device revealed an in-progress compromise by an advanced threat actor we later attributed to RansomHub affiliates.
Over the next 48 hours, our team worked closely with the customer to investigate, hunt, contain, and remediate the threat before it could become ransomware.
Due to our team's advanced intervention capabilities, we secured the customer’s network with zero business downtime. Continue reading to see how the incident started.
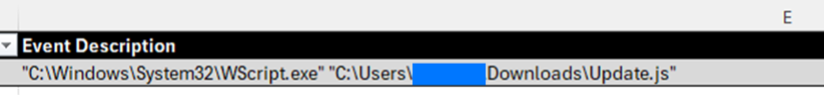
The incident started when a user downloaded and subsequently executed a file that they were led to believe was a legitimate browser update. In this case, it was a malicious JavaScript payload.
The download kicked off a chain of automated reconnaissance and initial command and control activity, including enumerating Active Directory users and computers, querying key local system information, hunting for credentials in memory, and various other discovery techniques.
Within minutes, second-stage malware was deployed as a recurring Scheduled Task for persistence. Following this, a legitimate Python distribution was downloaded to % LOCALAPPDATA%ConnectedDevicesPlatform, along with an encrypted Python script that served as a SOCKS proxy with attacker infrastructure, exposing the corporate network directly over the Internet.
The encrypted script was protected by an unpacking routine consisting of 10 layers of multi-stage encryption, with each stage unpacking the next along with other components.
Each level of the decryption process had randomized variable names designed to thwart unpacking attempts. Additionally, each stage attempted to implement basic anti-analysis techniques, including VM detection, Debug detection, and Process Tracing detection.
Our team wrote an unpacking routine for this specific variant to assist us in retrieving the final payload in plaintext. If you are a Varonis customer and need help with this task, please contact our IR team.
The final payload was a SOCKS proxy designed to facilitate communication between attacker endpoints and internal network infrastructure using the compromised host as a transport pivot.
Source: BleepingComputer



