Cyber: One Threat Actor Responsible For 83% Of Recent Ivanti RCE Attacks
Threat intelligence observations show that a single threat actor is responsible for most of the active exploitation of two critical vulnerabilities in Ivanti Endpoint Manager Mobile (EPMM), tracked as CVE-2026-21962 and CVE-2026-24061.
The security issues have been flagged as actively exploited in zero-day attacks in Ivanti's security advisory, where the company also announced hotfixes.
Both flaws received a critical severity rating and allow an attacker to inject code without authentication, leading to remote code execution (RCE) on vulnerable systems.
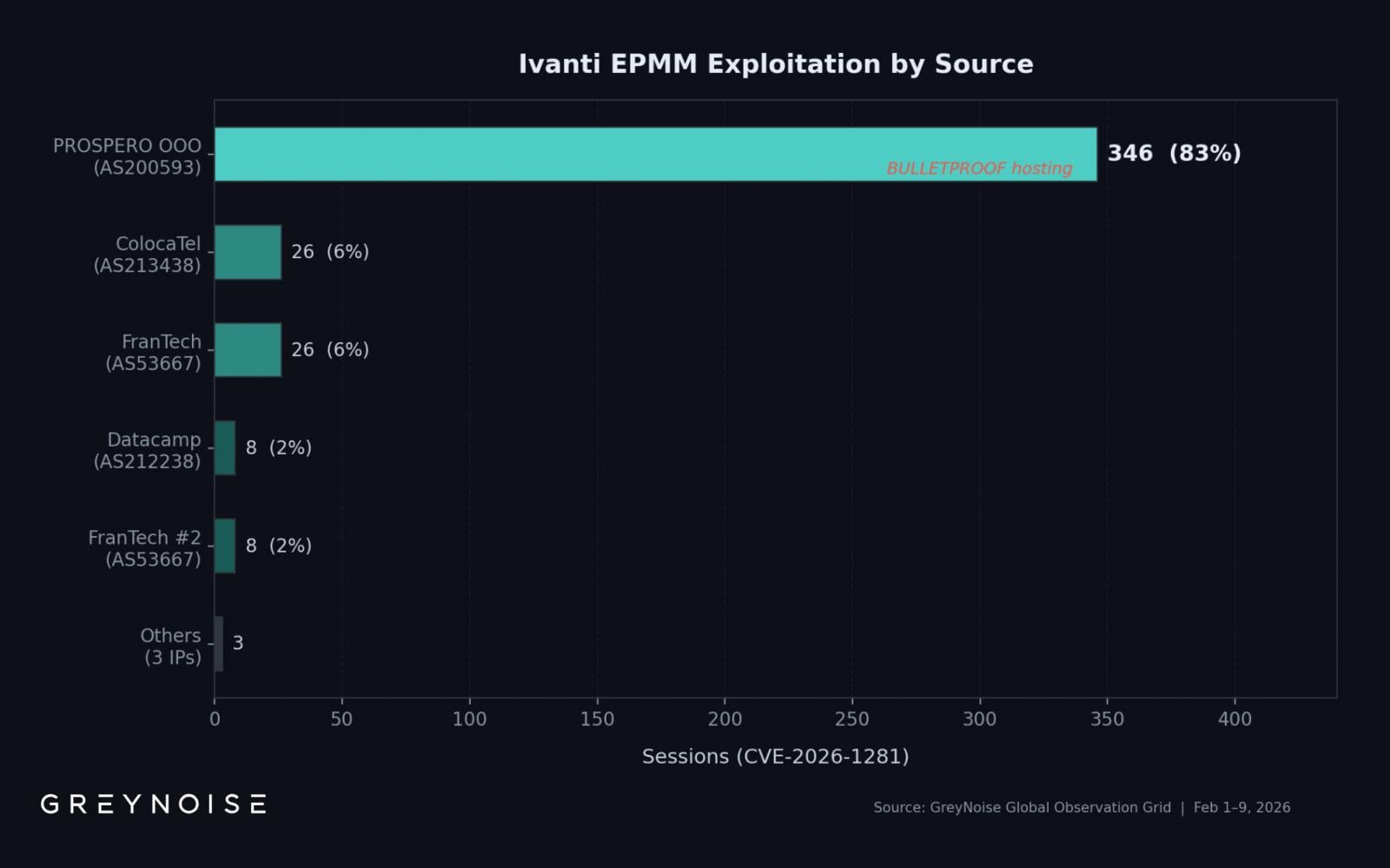
A single IP address hosted on bulletproof infrastructure is responsible for over 83% of exploitation activity related to the two vulnerabilities, says threat-focused internet intelligence company GreyNoise.
Between February 1st and 9th, the monitoring platform observed 417 exploitation sessions originating from 8 unique source IP addresses, and centered on CVE-2026-21962 and CVE-2026-24061.
The highest volume, 83%, comes from 193[.]24[.]123[.]42, hosted by PROSPERO OOO (AS200593), which Censys analysts marked as a bulletproof autonomous system used to target various software products.
A sharp spike occurred on February 8, with 269 recorded sessions in a single day. The figure is almost 13 times the daily average of 22 sessions, GreyNoise noted.
Of the 417 exploitation sessions, 354 (85%) used OAST-style DNS callbacks to verify command execution capability, pointing to initial access broker activity.
Interestingly, several published indicators of compromise (IoCs) include IP addresses for Windscribe VPN (185[.]212[.]171[.]0/24) present in GreyNoise telemetry as scanning Oracle WebLogic instances, but no Ivanti exploitation activity.
The researchers note that the PROSPERO OOO IP address they saw "is not on widely published IOC lists, meaning defenders blocking only published indicators are likely missing the dominant exploitation source."
Source: BleepingComputer



