Cyber: Security When Identity Isn’t The Weak Link, Access Still Is
For years, identity has been treated as the foundation of workforce security. If an organization could reliably confirm who a user was, the assumption followed that access could be granted with confidence.
That logic worked when employees accessed corporate networks from corporate devices under predictable conditions. Today, that no longer reflects how access is actually used or abused.
The modern workforce operates across multiple locations, networks, and time zones. Employees routinely switch between corporate laptops, personal devices, and third-party endpoints.
Access is no longer anchored to a single environment or device, yet security teams are expected to support this flexibility without increasing exposure or disrupting productivity, even as the signals used to make access decisions become noisier, more fragmented, and harder to trust on their own.
As a result, identity is being asked to carry responsibility it was never designed to hold alone. Authentication can confirm who a user claims to be, but it does not provide sufficient insight into how risky that access may be once device condition and context are taken into account. In modern environments, the core issue is not identity failure, but the over-reliance on identity as a proxy for trust.
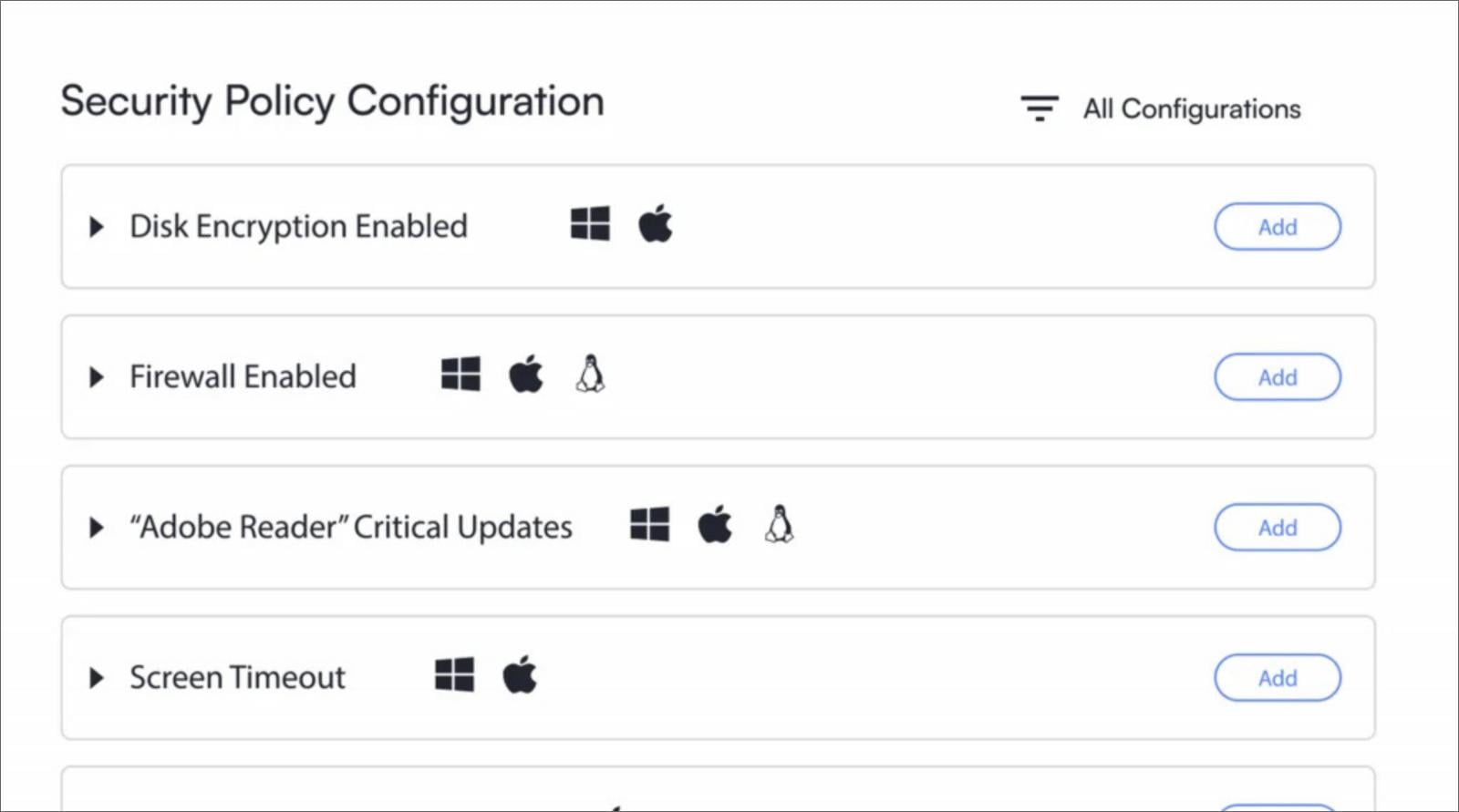
A legitimate user accessing systems from a secure, compliant device represents a fundamentally different risk from the same user connecting from an outdated, unmanaged, or compromised endpoint. Yet many access models continue to treat these scenarios as equivalent, granting access primarily on identity while device condition remains secondary or static.
This approach fails to account for how quickly device risk changes after authentication. Endpoints regularly shift state as configurations drift, security controls are disabled, or updates are delayed, often long after access has already been granted.
When access decisions remain tied to the conditions present at login, trust persists even as the underlying risk profile degrades.
These gaps are most visible across access paths that fall outside modern conditional access coverage, including legacy protocols, remote access tools, and non-browser-based workflows. In these cases, access decisions are often made with limited context, and trust is extended beyond the point where it is justified.
Attackers are increasingly exploiting these blind spots by reusing misplaced trust rather than breaking authentication, stealing session tokens, abusing compromis
Source: BleepingComputer



