Cyber: Complete Guide to Telegram Mini Apps abused for crypto scams, Android malware delivery
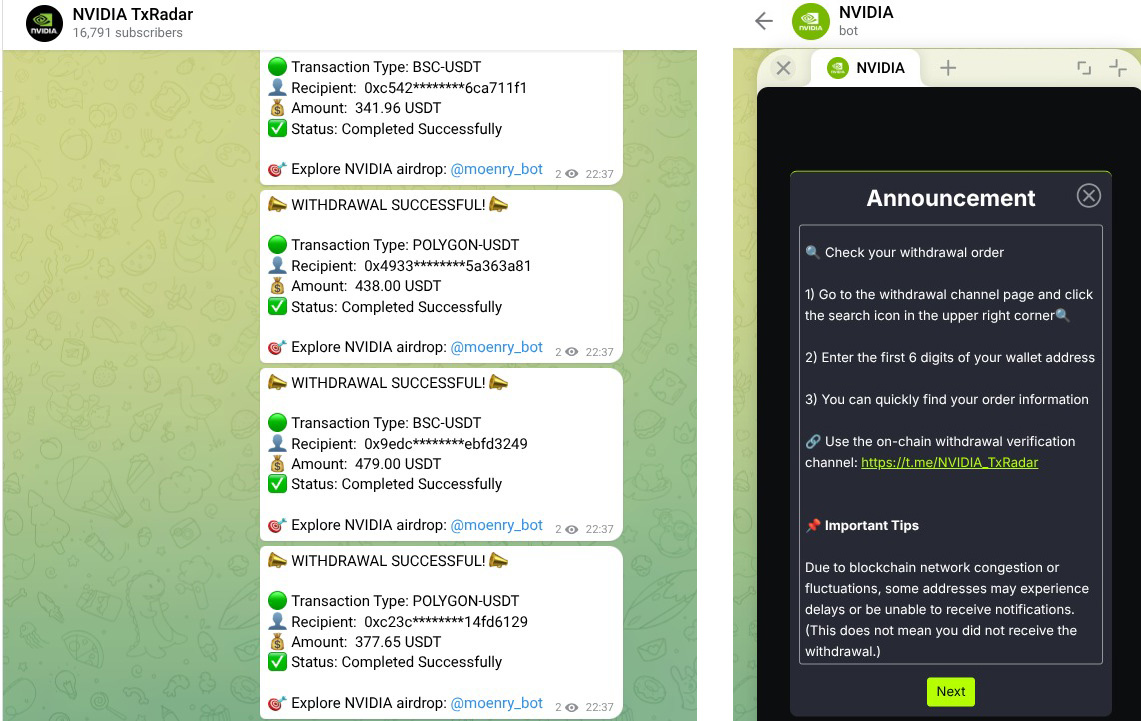
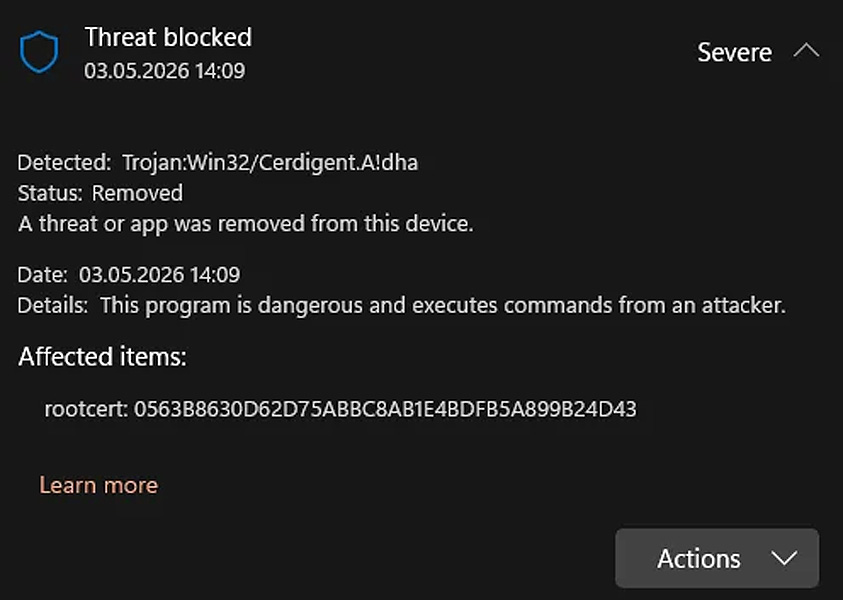
Cybersecurity researchers have uncovered a large-scale fraud operation that uses Telegram’s Mini App feature to run crypto scams, impersonate well-known brands, and distribute Android malware. A new report by CTM360 says the platform, dubbed FEMITBOT, is based on a string found in API responses and uses Telegram bots and embedded Mini Apps to create convincing, app-like experiences directly within the messaging platform. Telegram Mini Apps are lightweight web applications that run inside Telegram’s built-in browser, enabling services such as payments, account access, and interactive tools without requiring users to leave the app. According to a CTM360 report shared with BleepingComputer, the FEMITBOT platform is used to conduct multiple types of scams, including fake cryptocurrency platforms, financial services, AI tools, and streaming sites. In various campaigns, threat actors impersonated widely recognized brands to increase credibility and engagement, while using the same backend infrastructure with different domains and Telegram bots. Some of the brands impersonated in this campaign include Apple, Coca-Cola, Disney, eBay, IBM, Moon Pay, NVIDIA, YouKu, Researchers say the activity uses a shared backend, where multiple phishing domains use the same API response, "Welcome to join the FEMITBOT platform," indicating they are all using the same infrastructure. The operation uses Telegram bots to display phishing sites directly within the social media platform. When a user interacts with a bot and clicks "Start," the bot launches a Mini App that displays a phishing page in Telegram’s built-in WebView, making it appear as part of the app itself.
Source: BleepingComputer