Cyber: Report: CISA Adds Actively Exploited Linux Root Access Bug CVE-2026-31431 to KEV

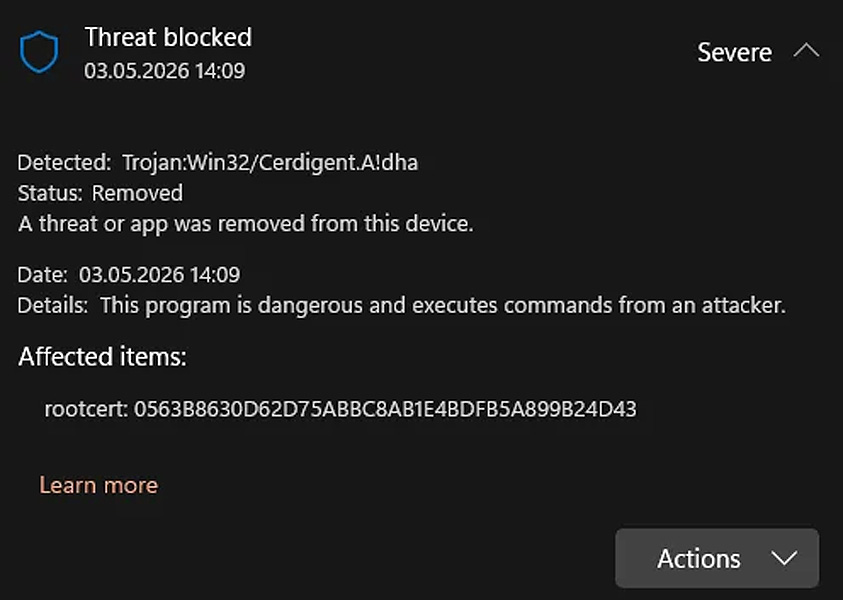
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Friday added a recently disclosed security flaw impacting various Linux distributions to its Known Exploited Vulnerabilities (KEV) catalog, citing evidence of active exploitation in the wild. The vulnerability, tracked as CVE-2026-31431 (CVSS score: 7.8), is a case of local privilege escalation (LPE) flaw that could allow an unprivileged local user to obtain root. The nine-year-old flaw is also tracked as Copy Fail by Theori and Xint. Fixes have been made available in Linux kernel versions 6.18.22, 6.19.12, and 7.0. "Linux Kernel contains an incorrect resource transfer between spheres vulnerability that could allow for privilege escalation," CISA said in an advisory. In a write-up published earlier this week, the researchers said Copy Fail is the result of a logic bug in the Linux kernel's authentication cryptographic template that allows an attacker to reliably trigger privilege escalation trivially by means of a 732-byte Python-based exploit. It was introduced through three separate, individually harmless changes to the Linux kernel made in 2011, 2015, and 2017. The high-severity security vulnerability impacts Linux distributions shipped since 2017, and permits an unprivileged local user to obtain root-level access by corrupting the kernel's in-memory page cache of any readable file, including setuid binaries. This corruption could be carried out by unprivileged users and could result in code execution with root permissions. "Because the page cache represents the in-memory version of executables, modifying it effectively alters binaries at execution time without touching disk," Google-owned Wiz said. "This enables attackers to inject code into privileged binaries (e.g., /usr/bin/su) and thereby gain root privileges." The prevalence of Linux in cloud environments means the vulnerability has a significant impact. Kaspersky, in its analysis of the flaw, said Copy Fail poses a serious risk to co
Source: The Hacker News